When installing Linux on a computer, I always install a program called sl. This program displays a train when you execute sl. It is not a practical program but rather a program that gives you time to think when you make a typo with the commonly used ls command in the terminal. Showing a train on the screen helps you calm down and not make other mistakes when you are in a hurry to type. That's why I install this program.
 |
| source: https://github.com/mtoyoda/sl |
The terminal is a program that receives and displays two streams, stdout, and stderr, from a program. These outputs are sequential outputs and typically flow from the top left to the bottom right. However, to draw new characters on an already-used screen, a special method is needed. This special method is called escape codes.
Escape codes are a kind of promise defined in the terminal. Currently, these promises follow the standards defined in ISO 6429. However, in the past, there was no unified consensus, and each terminal had different rules. Understanding this may require knowledge of computer history.
Today, the term "terminal" means an application for the command-line interface(CLI). However, in the past, a terminal was literally the endpoint device of a computer. This terminal was connected to a mainframe computer and was responsible for its input/output. The reason that modern terminal apps are called "terminal emulators" is that they emulate these old-age terminal devices. Terminals were manufactured by various companies. For instance, ADM-3A, IBM's IBM 2260, and IBM 3270, and the VT series of DEC, which was later merged with HP. Each had its own standards for controlling terminals.
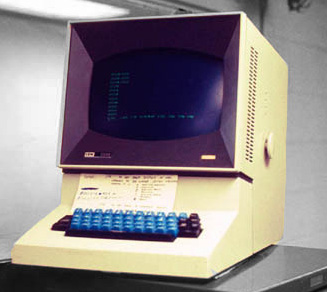 |
| source: https://en.wikipedia.org/wiki/IBM_2260 |
Escape codes were not compatible across different terminals; efforts to standardize them began in the 1970s. The first standard was ECMA-48, which was first published in 1976. However, the biggest impact on modern escape codes was the VT100, produced by DEC in 1978. The VT100 introduced the Control Sequence Introducer(CSI) and various commands, including important functions such as cursor movement and scrolling, which are still used in modern terminal emulators. Based on the implementation of the VT100, ANSI released the ANSI X3.64 standard in 1979, and in 1983, ISO published ISO 6429 based on ECMA-48 and ANSI X3.64. In 1992, some codes are added. All modern terminal emulators implement escape codes based on ISO 6429.
Comments
Post a Comment